Getting started
Overview
Today, many web applications experience high traffic demands and traffic spikes can lead to server overloads and a deteriorating user experience.
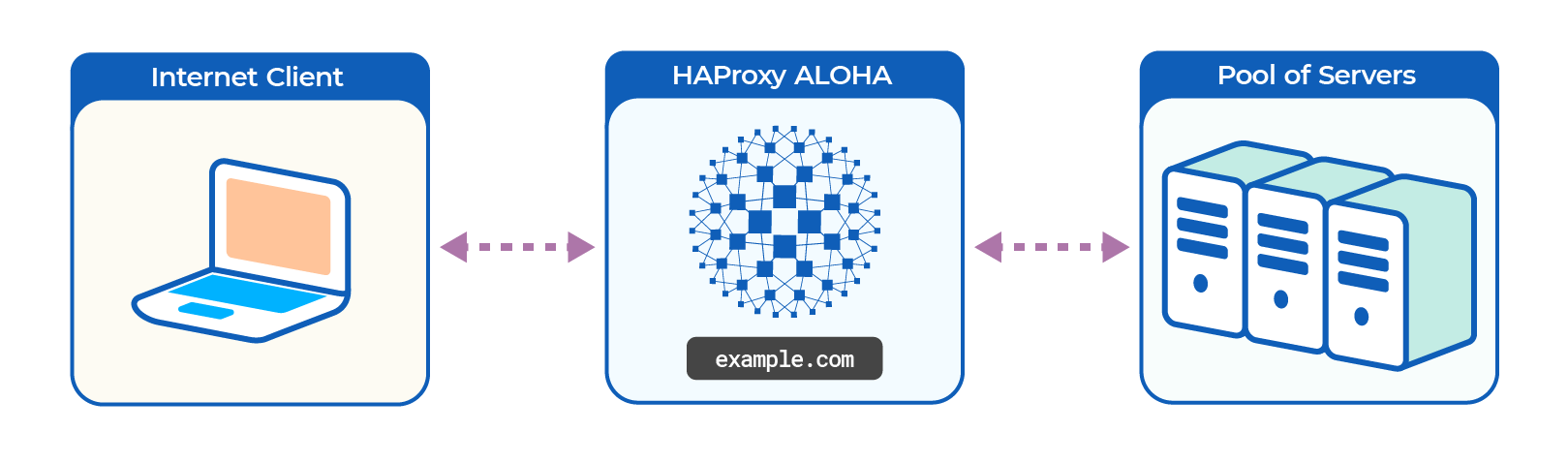
HAProxy ALOHA appliances spread traffic across a pool of healthy servers, allowing you to scale out your capacity for handling concurrent requests. You can then easily answer the demand, while also improving performance and availability.
You can seamlessly integrate HAProxy ALOHA with your existing infrastructure at the edge of your network, either as a hardware or as a virtual appliance.
The job of a load balancer Jump to heading
A load balancer sits in front of your web servers and receives requests directly from clients before relaying them to one of your servers. In this way, it can distribute requests evenly, allowing the work to be shared. This prevents any backend server from becoming overworked and, as a result, your servers operate more efficiently. A load balancer differs from a web or application server in that it does not host your web application directly. Instead, its job is to spread the work across your cluster of servers.
HAProxy ALOHA features Jump to heading
HAProxy ALOHA provides security and management features in addition to load balancing. You can use it to load balance any TCP/IP service including databases, message queues, mail servers, and IoT devices.
HAProxy ALOHA offers traffic rate limiting, health checks, switching rules (ACLs), an optional Web Application Firewall, application-layer DDoS attack protection, SSL termination, HTTP compression, and best-in-class observability.
Hardware HAProxy ALOHA appliances feature PacketShield, which provides stateful packet filtering and enhanced protection against DDoS attacks.
HAProxy ALOHA flow manager and Linux Virtual Server Jump to heading
In addition to the HAProxy ALOHA layer 7 reverse proxy described above, HAProxy ALOHA supports an alternative architecture composed of the HAProxy flow manager and the Linux Virtual Server (LVS) load balancer.
The flow manager serves as a firewall capable of filtering incoming packets based on NIC interface, protocol, and IP address/port (both source and destination). It can then apply policies such as allow, drop, forward to an LVS director, or route according to a routing table.
Linux Virtual Server (LVS) is an open-source component that provides load balancing at layer 4. It supports a variety of load balancing algorithms, health check features, and more.
Do you have any suggestions on how we can improve the content of this page?