PacketShield
LVS and Synproxy
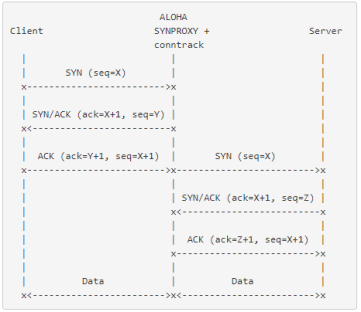
The SYNPROXY module deploys TCP SYN cookies to establish a TCP connection terminated on a third party device located behind the HAProxy ALOHA. It relies on the conntrack module to translate sequence numbers.
The diagram below show how sequence numbers are translated from Y (client to HAProxy ALOHA) to Z (HAProxy ALOHA to server):
Objective Jump to heading
In HAProxy ALOHA, the SYNPROXY module is mainly used for integration with PacketShield to provide protection against packet flood attacks in the following cases:
-
Traffic routed through HAProxy ALOHA
-
Load balancing at Layer 4 in NAT mode
-
Load balancing at Layer 4 in DSR mode if the server-to-client traffic is routed through HAProxy ALOHA
Info
PacketShield requires the TCP connection to terminate locally, which the SYNPROXY module emulates.
Configuring TCP SYNPROXY Jump to heading
Requirements Jump to heading
Configure the conntrack module Jump to heading
In the HAProxy ALOHA Services tab, edit the service settings to add the following setting to the conntrack service:
text
text
Info
The conntrack service is accessible in the advanced mode.
The sysctl prevents conntrack from accepting packets as NEW packets and allowing SYNPROXY to work.
Configure LVS Jump to heading
With LVS, the use of the SYNPROXY module leads to a SYN/SYN-ACK loop between clients and the load balancer.
To circumvent this issue, we use LVS in conjunction with conntrack.
-
In the HAProxy ALOHA Services tab, edit the service settings to add the following setting to the LVS service:
textconntracktextconntrack
SYNPROXY syntax rule Jump to heading
text
text
Available chains Jump to heading
| Chain | Description |
|---|---|
<input> |
protect local or LVS connections |
<forward> |
protect a connection routed through HAProxy ALOHA |
Conditions of application Jump to heading
| Condition | Description |
|---|---|
[[not] dst <host>] |
IP packet destination IP or subnet |
[[not] iface <interface>] |
inbound network interface (should match PacketShield interface) |
[[not] dstport <port>] |
IP packet destination port (range accepted) |
TCP options Jump to heading
| Option | Description |
|---|---|
[wscale <value>] |
Windows scale. Default value: not set. Requires timestamp. |
[mss <value>] |
Maximum Segment Size. Default value: 1460. |
[sack-perm] |
Selective Acknowledgment. Default value: not enabled. Requires timestamp. |
[timestamp] |
Timestamps. Default value: not enabled. |
[ecn] |
Explicit Congestion Notification. Default value: not enabled. Requires timestamp. |
Info
TCP options are ignored when SYNPROXY module is used with PacketShield. In this case, PacketShield TCP options are used.
Configuring SYNPROXY module Jump to heading
-
In the HAProxy ALOHA Services tab, edit a service configuration.
-
In the text area, create your rules.
Configuration examples Jump to heading
Protect HTTP and HTTPs services managed by HAProxy or LVS running in HAProxy ALOHA:
text
text
Protect HTTP and HTTPs services hosted by cloud service VMs located behind HAProxy ALOHA:
text
text
Do you have any suggestions on how we can improve the content of this page?